Understanding SAP Configuration & Security Analysis
Introduction
In the ever-evolving digital landscape, organizations face an increasing number of cyber threats that can compromise their sensitive data, disrupt operations, and damage their reputation. To mitigate these risks and ensure the security of SAP system landscapes, it is crucial for organizations to stay ahead of cyber threats through effective SAP configuration and security practices. In this blog, we will explore the significance of SAP configuration and security analysis, its key components, the benefits it brings to organizations, and best practices to implement.
What is SAP Configuration & Security Analysis?
Configuration & Security Analysis (CSA) within SAP Focused Run ensures transparency and compliance in SAP system landscapes. It provides comprehensive central governance for software levels, patches, critical authorizations, and configuration settings across the entire landscape. CSA offers a highly scalable approach to compare the desired state (TO-BE) with the current state (AS-IS), allowing organizations to identify deviations, security vulnerabilities, and configuration changes that may impact the overall SAP landscape security.
Key Components of SAP Configuration and Security Analysis
Validation:
Validation is a crucial component of SAP CSA, allowing organizations to assess the homogeneity of system configurations. It involves comparing the actual configuration data against predefined policies or benchmarks. By performing validation checks, organizations gain insights into the compliance level of their SAP systems and identify areas that require attention or remediation. Validation reports provide valuable information for auditing, compliance tracking, and security improvement initiatives.
Policy Management:
Policy Management is a vital aspect of CSA and involves the definition and management of validation rules. It comprises two types of policies: Single Policies and Composite Policies. Single Policies store validation rules in XML files, organized by checks and configurations to be validated. Composite Policies allow the combination of multiple policies to provide comprehensive analysis and reporting capabilities. Policy Management ensures that organizations can establish and enforce security baselines and best practices across their SAP system landscapes.
Policy Catalog:
The Policy Directory enables a seamless implementation of pre-set XML policies, eliminating the need for detailed comprehension of policy syntax or structure. The concept behind the Policy Directory is to import policies from an external data source, choose the appropriate checks, and convert them into active policies for verification and reporting purposes. This can be beneficial if you're looking to establish an internal policy check database within your corporation.
Alert Management for Configuration Validation:
The purpose of managing alerts for configuration validation is to establish alert settings that are based on the outcomes of validation or modifications in store content. The Alert Source delineates whether a policy or a configuration store can be chosen. The chosen policy sets the criteria for the validation process. These policies comprise checks that stipulate rules to confirm whether configuration items are compliant or non-compliant. Alerts concerning non-compliant outcomes at the system, configuration store, check, or item level are forwarded to 'Alert Management'.
Changes:
Changes tracking and analysis is an essential feature of CSA. It captures and reports configuration changes made in managed systems. By maintaining a historical record of changes, organizations can easily identify modifications, compare system behavior over time, and investigate any discrepancies or issues that may arise. This component is instrumental in identifying the root cause of problems, understanding system behavior, and maintaining the integrity of system configurations.
Search:
The Search functionality within CSA enables users to locate specific configuration items by searching for particular strings or patterns. It provides a flexible and efficient way to find relevant information within the vast configuration dataset. Whether searching for specific system parameters, authorizations, or other configuration details, the Search feature simplifies the process of locating critical information, saving time and effort for administrators and auditors.
Store Browser and Config Stores:
Configuration details in SAP Focused Run are stored in containers called Config Stores within the Configuration and Change Database (CCDB). The Store Browser provides a centralized view of these stores, allowing users to navigate and explore the stored configuration data. It offers a comprehensive overview of technical systems, their associated config stores, and the respective configuration items. The Store Browser enables administrators and security teams to analyze system configurations, track changes, and investigate specific items or stores as needed.
Benefits of SAP Configuration and Security Analysis
Strengthened Cybersecurity:
By leveraging SAP Configuration and Security Analysis, organizations can effectively safeguard their SAP systems against potential cyber threats. CSA provides insights into vulnerabilities, enforces security baselines, and ensures compliance with security standards and regulations. It allows organizations to detect and address security risks proactively, minimizing the potential for data breaches, unauthorized access, or system compromise. CSA empowers organizations to adopt a proactive cybersecurity approach and stay one step ahead of malicious actors.
Enhanced Compliance:
Compliance with industry standards and regulations is a critical concern for organizations operating in various sectors. CSA assists organizations in maintaining compliance by continuously monitoring and validating system configurations against predefined policies. It generates compliance reports that provide evidence of adherence to security best practices and regulatory requirements. These reports play a crucial role during audits, demonstrating a proactive approach to security and compliance.
Improved Operational Efficiency:
SAP Focused Run for SAP Solution Manager offers guided procedures for CSA-specific activities, automating and streamlining the configuration and security analysis processes. Guided procedures enable standardized execution of tasks, reducing manual effort and enhancing operational efficiency. By automating policy validation, result distribution, and related activities, organizations can save time, improve productivity, and focus on critical security issues, remediation efforts, and proactive measures.
Reduced Business Risks:
Implementing SAP Configuration and Security Analysis (CSA) significantly reduces business risks associated with system vulnerabilities and mis configurations. By identifying deviations and potential security weaknesses, organizations can take timely corrective actions, mitigating the risks of system disruptions, unauthorized access, and data breaches. CSA ensures the integrity, confidentiality, and availability of critical business data, protecting organizations from financial losses, reputational damage, and legal consequences.
Proactive Maintenance and Planning:
CSA provides valuable insights into the health and stability of SAP system landscapes. By continuously monitoring configurations and identifying potential risks, organizations can proactively plan maintenance activities, patch management, and system upgrades. CSA helps organizations stay current with the latest security patches, reducing the vulnerability exposure window and ensuring the overall stability and reliability of their SAP systems.
Best Practices for SAP Configuration and Security Analysis
Define and Implement Security Baselines
Establishing security baselines tailored to the organization's specific needs is essential. This includes defining policies, checks, and configurations that align with industry standards and best practices. Organizations should collaborate with their security teams and subject matter experts to create comprehensive security baselines that address critical areas such as user authorizations, system parameters, and communication settings.
Regularly Perform Configuration Validations
Regular configuration validations are key to maintaining the security and compliance of SAP systems. Organizations should define a frequency for performing validations, ensuring that they cover all critical areas and systems. Regular validations provide early detection of configuration deviations, security vulnerabilities, and unauthorized changes, allowing organizations to take prompt corrective actions.
Actively Monitor Changes
Monitoring and analyzing system changes are essential for maintaining the integrity of SAP configurations. Organizations should enable change tracking and establish processes to review and investigate changes regularly. This includes capturing change details, analyzing change logs, and identifying any unusual or unauthorized modifications. Active monitoring of changes helps identify potential security breaches, system performance issues, and misconfigurations.
Conduct Periodic Audits and Assessments
Periodic audits and assessments are crucial to evaluate the effectiveness of SAP configuration and security analysis practices. Organizations should conduct internal or external audits to validate the compliance of systems with security standards and regulations. These audits help identify areas for improvement, provide valuable insights into the effectiveness of security controls, and ensure continuous enhancement of security practices.
Stay Informed about Security Updates
Staying updated with the latest security patches, vulnerabilities, and industry trends is essential for effective SAP configuration and security analysis. Organizations should establish processes to monitor and evaluate security bulletins, vendor advisories, and other sources of security information. This helps organizations proactively address emerging threats, implement necessary patches, and maintain an agile and secure SAP system landscape.
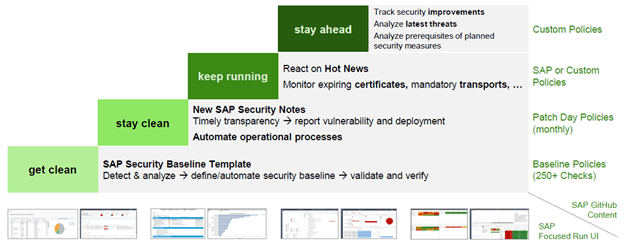
SAP CSA Best Practice
Best Practice Guides are available to help you make use of the full capabilities of Configuration and Security Analytics in SAP Focused Run. The set of documents is continually enhanced based on new product features and project experience.
It is possible to enhance CCDB Config Stores, Please note that CCDB and the CSA applications are developed for technical configuration data. It is not supposed to store and display a high number of records per config store.
Updated list of available config stores can be found here
SAP Delivered CSA Policies
SAP GitHub project provides policies for Focused Run - Advanced Configuration Monitoring - Configuration and Security Analytics. These policies are the basis for validating configuration items of systems which are stored centrally in Focused Run. Policies comprise of a set of rules which are ideally derived from a hardening guide or a system baseline documentation.
For more information visit here to get an updated list of SAP delivered policies.
CSA Plug-Ins for Guided Procedures
Focused Run for SAP Solution Manager provides Guided Procedures to support standardized execution of regular tasks. Guided procedures may include automated or manual activities.
For many different tasks SAP provides activity plug-ins for re-use. These plug-ins help you to develop your own guided procedures that include tailored, automatic activities. These activities can be triggered manually or executed entirely in the background as part of an alert reaction, service level reporting, health check guided or regular operational task procedure.
CSA Guided Procedures can do some of the below activities to name a few:
• Automatic execution of the CSA policy validation
• Distribution of validation results via mail
• Distributed result can be configured regarding 'Validation result only' (with link to CSA), 'Only Non- Compliant items' or 'All compliance items'
Complete list of Activity Plug-ins can be found here
Conclusion:
In an era of evolving cyber threats, organizations must prioritize SAP configuration and security analysis to protect their valuable data, ensure compliance, and minimize business risks. By understanding the significance of SAP CSA, leveraging its key components, and following best practices, organizations can establish a robust security framework, stay ahead of cyber threats, and safeguard their SAP system landscapes effectively.